Outsourced Bookkeeping Security: How Accounting Firms Add Capacity Without Giving Away Client Data

Outsourced bookkeeping security is the real objection, not outsourcing itself
When accounting firm leaders search for outsourced bookkeeping security, outsourced accounting security, offshore bookkeeping security, or how to outsource bookkeeping without losing control, they are usually not debating whether outside capacity is useful.
They already know it is useful.
The real question is whether the firm can add outsourced or extended staff without creating a security problem around client data, bank statements, journal activity, and portal access.
That concern is rational. The firm still owns the client relationship, the deliverable quality, and the reputational risk. If outsourced bookkeepers can see every client, if staff share logins, or if no one can explain who changed what, the firm has taken on operational risk in exchange for short-term capacity.
That is why the best outsourced bookkeeping workflow is not just about labor cost or turnaround time. It is about control.
Wesley for accounting firms gives firms a way to add outsourced, offshore, seasonal, or contractor capacity inside a controlled operating system instead of relying on informal access and inbox habits.
Choose your workflow
Tax workflow hub
The full cluster for W-9 collection, 1099 review, and filing-season cleanup workflows.
Collect a W-9 before filing a 1099
The cleanest timing and follow-up workflow before filing season turns reactive.
1099-K vs 1099-NEC
How to separate processor-reported payments from contractor compensation.
Why a contractor is missing from your QuickBooks 1099
A practical troubleshooting flow for inactive vendors, thresholds, and mapping issues.
Why credit card payments do not show up on 1099s
The exact reporting logic behind excluded card and payment-app transactions.
Coverage and resources
Open the authority pages that support this workflow.
Supported banks
See which institutions Wesley already covers and when statement fallback still matters.
Open page →
Integrations hub
See where Wesley fits before QuickBooks, Xero, QIF, Sage, and NetSuite workflows.
Open page →
Template library
Use saveable SOPs and checklists alongside the workflow pages.
Open page →
Why accounting firms worry about outsourced bookkeeping and data security
The most common fears are familiar to anyone who has tried to scale delivery with external help:
- outsourced staff can see more clients than they should
- shared credentials make offboarding messy and unsafe
- contractors get broad access instead of scoped access
- client portal permissions get mixed up with firm team permissions
- no one can prove who changed the books
- partner or manager review gets harder because the work trail is incomplete
Those are exactly the kinds of risks that make firms search for terms like secure outsourced bookkeeping, outsourced bookkeeping confidentiality, outsourced accounting access control, and accounting firm data security for offshore teams.
The useful framing is this: the problem is not that a task is outsourced. The problem is when outsourced work is handled without role boundaries, client boundaries, and an audit trail.
Add outsourced or seasonal staff as extended members, not as invisible operators
A secure outsourced bookkeeping workflow should start with team structure.
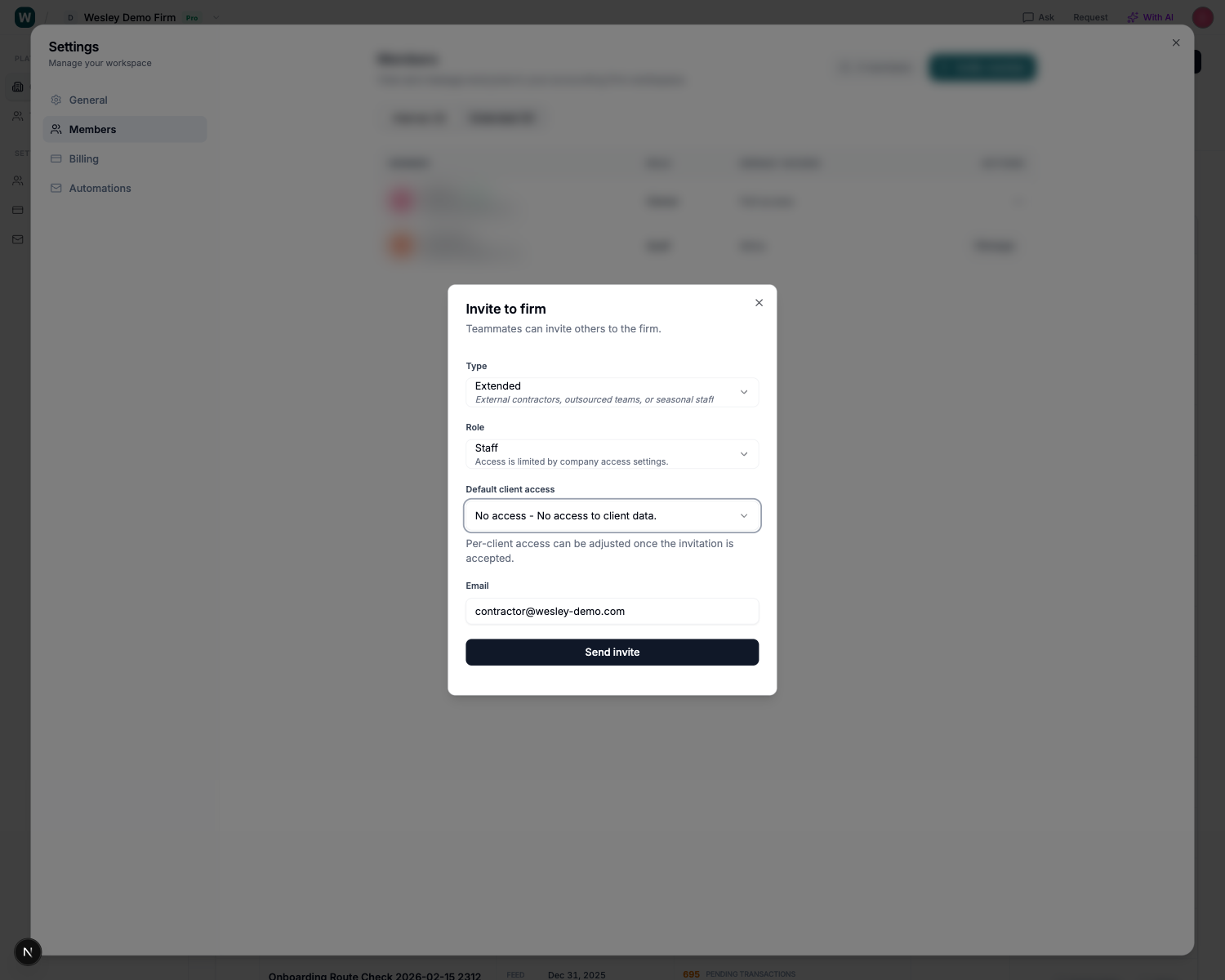
In Wesley, firms can separate internal staff from extended members. Extended is explicitly for external contractors, outsourced teams, or seasonal staff. That matters because it keeps the staffing model visible inside the system rather than burying it in email threads or shared accounts.
Then the firm can define a default access level for staff roles: write, read-only, or no access.
That makes a big difference in practice.
Instead of inviting outside help and figuring out the risk later, a firm can decide the control model up front:
- "No access" for people who should not see client data until the firm deliberately grants it
- "Read-only" for review, QA, or oversight workflows
- "Write" only where the person is expected to actually work in the books
This is one of the cleanest ways Wesley helps firms outsource bookkeeping without giving away unrestricted visibility.
Limit outsourced bookkeepers to the clients they actually handle
The next control layer is client assignment.
A lot of firms say they want outsourced bookkeeping security, but what they actually need is client-level scoping. If an outsourced bookkeeper is responsible for five clients, that person should not have accidental visibility into fifty.
In Wesley, client assignments are explicit, and the product makes the rule clear: only members with client access can be assigned.
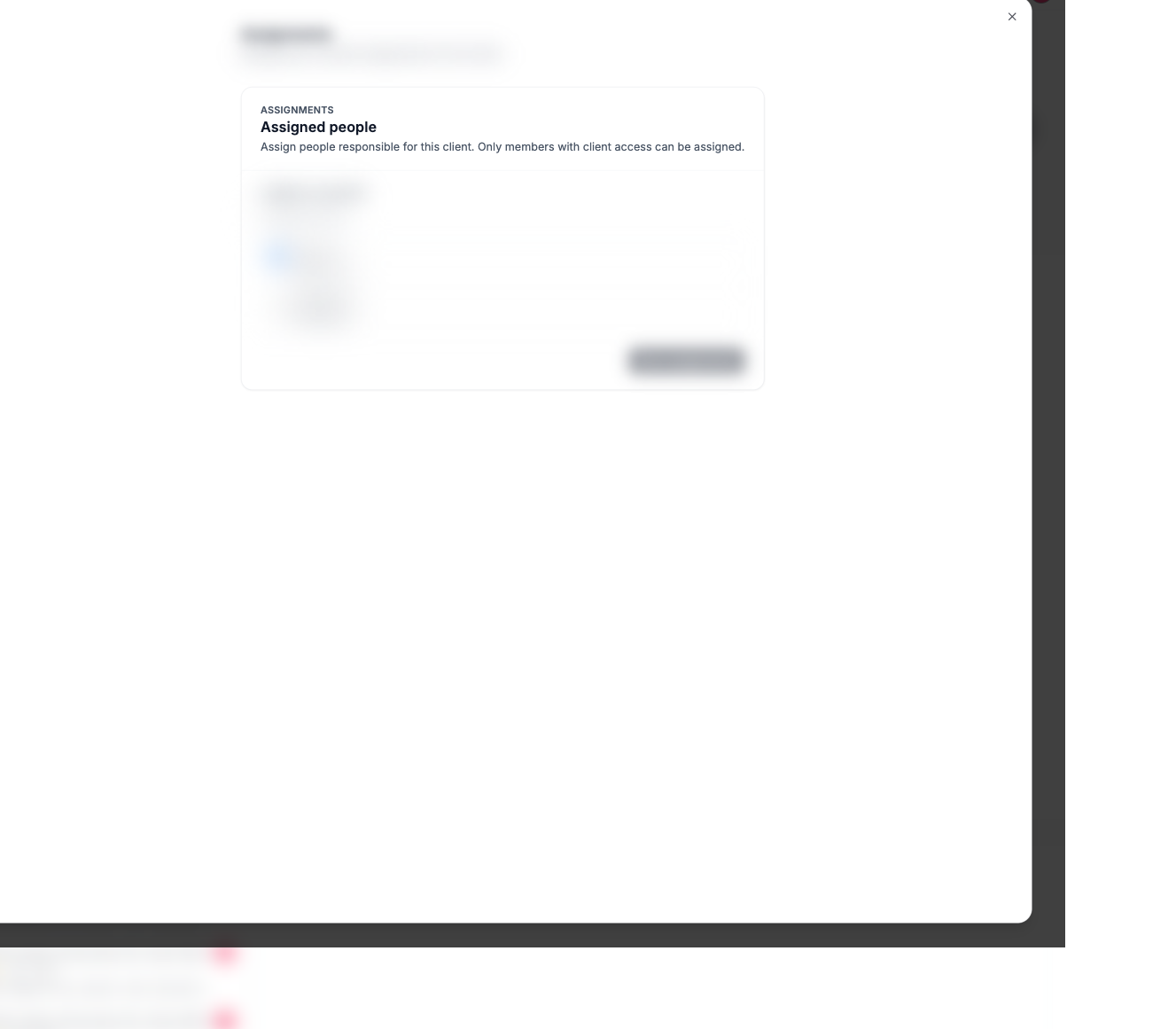
That is an important control for accounting firms because it turns a vague staffing model into an operational one:
- a reviewer can see which people are responsible for a client
- an outsourced staff member does not become a catch-all operator by default
- managers can change assignments without changing the entire firm structure
- access and responsibility stay aligned
This is the difference between “we work with an outsourced team” and “we can prove who has access to which client.”
If your firm is trying to build a secure outsourced accounting workflow, that distinction matters more than most teams realize.
Keep client portal access separate from outsourced team access
Another common security failure is mixing internal team access with client portal access.
Those are not the same thing. A contractor helping with bookkeeping should not automatically become the person who can invite or control client-facing portal users unless the firm intends that. Likewise, client-facing portal access should be managed separately from internal delivery staffing.
Wesley keeps client access as its own control surface inside the client settings area.
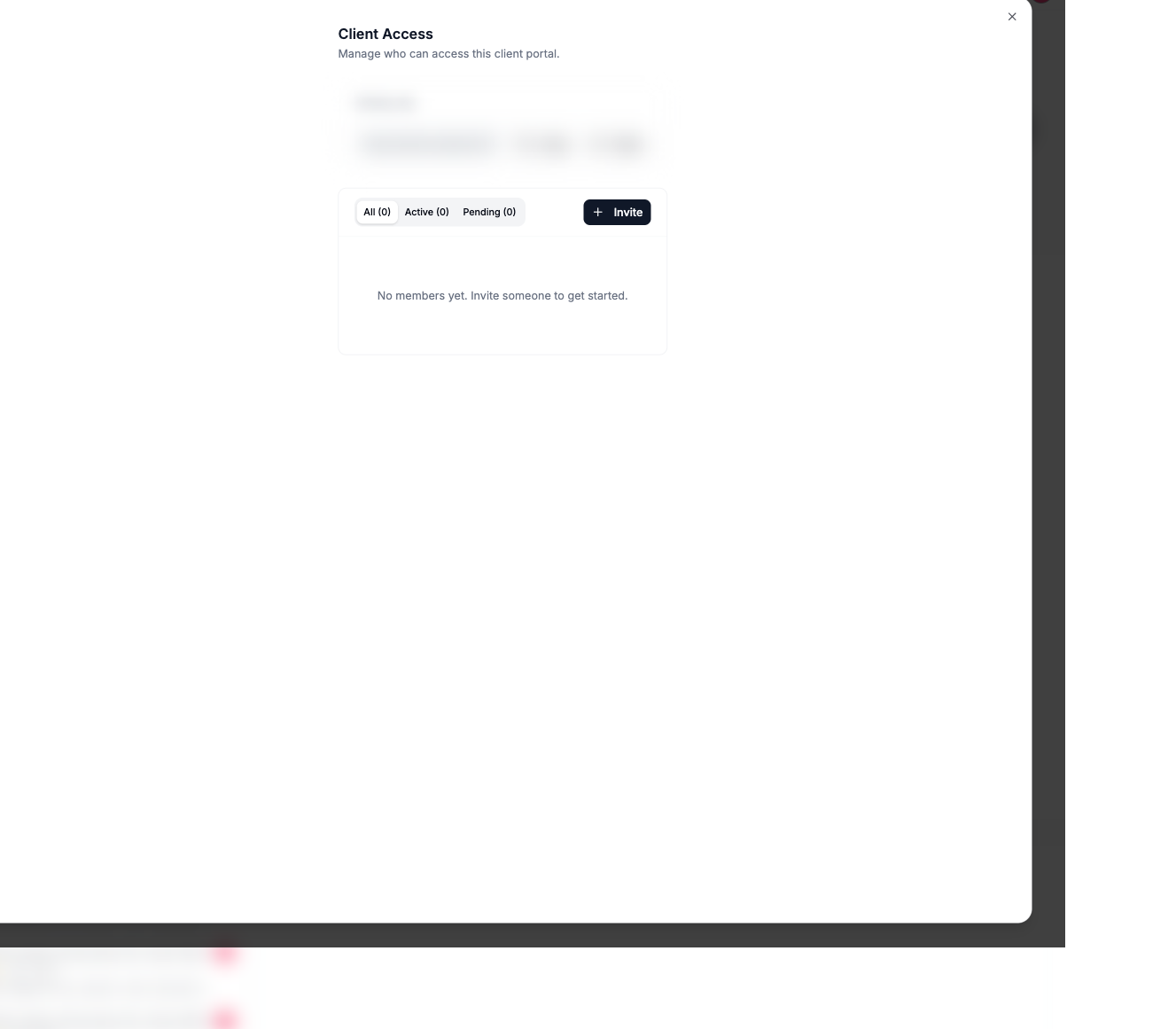
That separation is useful for accounting firms that want to outsource production work but keep tighter control over who interacts with the client-facing side of the system. It also makes it easier to explain your process to clients who ask how their data and access are handled.
When firms talk about outsourced bookkeeping data security, this is often what they mean in plain English: we want outsourced help, but we do not want to blur the line between internal work access and client-facing access.
Wesley gives the firm a clearer boundary.
Keep an audit trail when outsourced work touches the books
Access control is only half the story. The other half is traceability.
If an outsourced bookkeeper, a reviewer, a rules engine, or AI creates or changes entries, the firm needs a place to inspect that history. Otherwise the review process turns into guesswork.
Wesley includes audit log views at the client level so firms can track journal-related changes across imports, rules, AI activity, and manual edits.
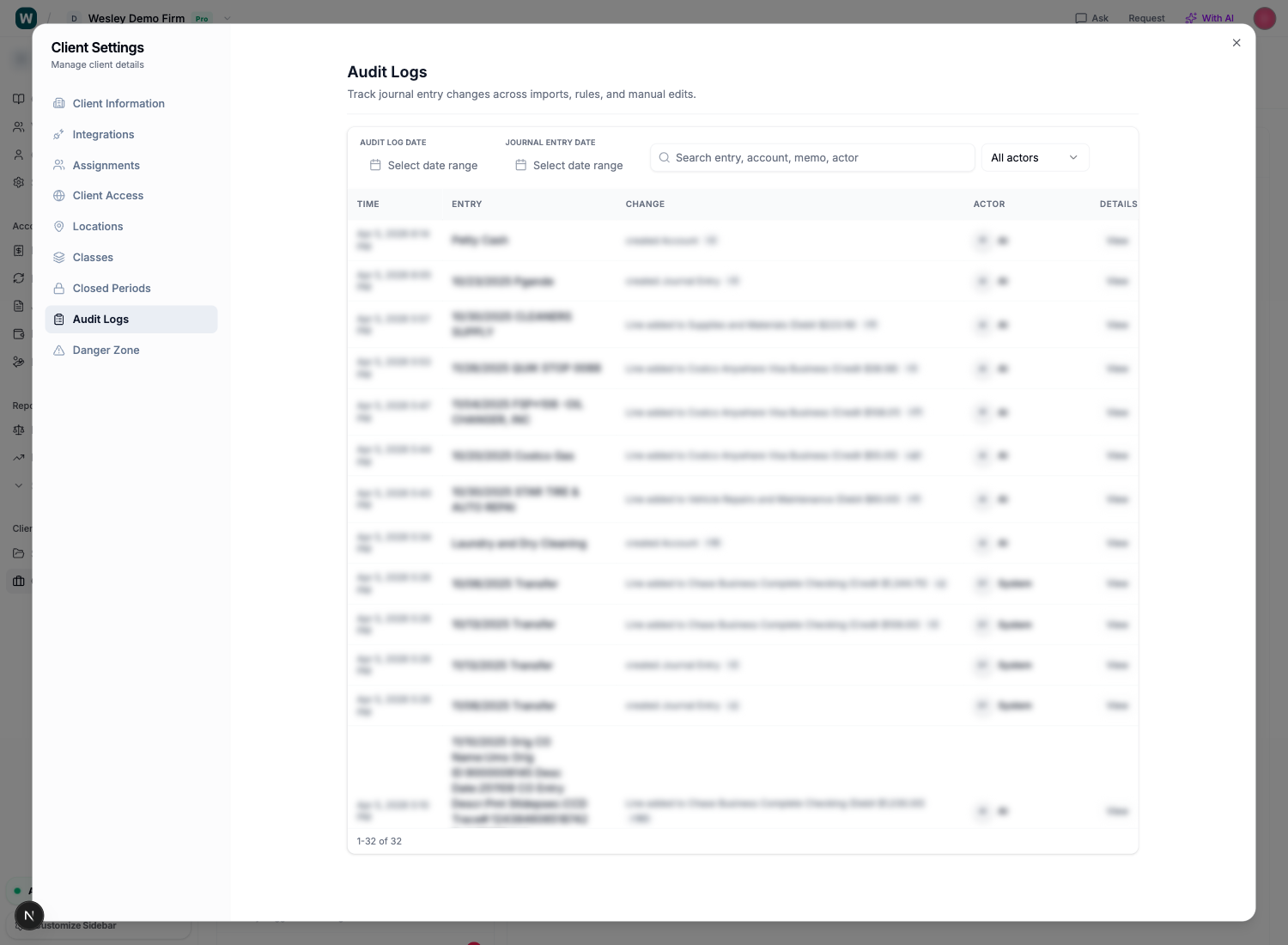
That matters for outsourced accounting security because an audit trail changes how review works:
- managers can see what changed instead of relying on memory
- unusual activity is easier to investigate
- firms can review outsourced output with more confidence
- offboarding is cleaner because accountability stays in the system, not in a former contractor's inbox or device
For firms comparing outsourced bookkeeping providers or building an offshore bookkeeping process in-house, this is one of the strongest control signals to look for.
What secure outsourced bookkeeping should look like in practice
A secure outsourcing workflow for an accounting firm usually looks like this:
- invite an external contractor or outsourced team member as "Extended"
- set their default access to "No access" or "Read-only" unless broader access is justified
- grant access only where the engagement requires it
- assign that person only to the clients they are responsible for
- keep client portal access separate from internal production access
- review the audit log when books are updated
That is a much stronger model than shared passwords, generic admin access, or ad hoc handoffs over email.
It also gives firms a better answer when clients ask about confidentiality and controls. The answer is no longer “don’t worry, we trust our outsourced team.” The answer becomes: here is how access is structured, limited, and tracked.
Why this matters for offshore bookkeeping and outsourced accounting growth
The reason this topic has so much search demand is simple: firms want the capacity benefits of outsourcing without the operational downside.
That means they need a system that supports both of these goals at the same time:
- grow delivery capacity with outsourced or seasonal help
- avoid turning client data access into a trust-based free-for-all
The firms that scale outsourced bookkeeping well usually do not win because they found cheaper labor. They win because they built a better control model around outside capacity.
That is the more durable way to think about Wesley. It does not just help firms process work faster. It helps them structure who can see what, who can act where, and how those actions are reviewed.
FAQ: outsourced bookkeeping security for accounting firms
Is outsourced bookkeeping secure for accounting firms?
It can be, but only if the firm uses proper access control, assignment boundaries, and audit trails. Outsourcing itself is not the risk. Uncontrolled access is the risk.
How can accounting firms outsource bookkeeping without giving access to every client?
Use role-based and client-based access together. A firm should be able to invite outsourced staff with no access or read-only access by default, then grant only the specific client access they need.
What is the difference between outsourced staff access and client portal access?
Outsourced staff access is internal firm access to bookkeeping work. Client portal access is client-facing access for portal users. They should be managed separately.
What should firms look for in outsourced accounting security?
Look for extended or contractor member types, read-only or no-access defaults, client-level assignments, clean offboarding, and audit logs that show who changed the books.
Why do firms worry about offshore bookkeeping security?
Because the firm still owns client trust, confidentiality, and review quality. Offshore or outsourced capacity only works well when the system preserves control over data access and change history.
Final takeaway
If your team is searching for outsourced bookkeeping security, secure outsourced accounting, or how to outsource bookkeeping without losing control, the answer is not to avoid outside capacity entirely.
The answer is to use a workflow that makes access explicit, limited, and reviewable.
With Wesley, firms can invite extended staff, set default access to write, read-only, or no access, assign outsourced team members only to the right clients, separate client portal access, and keep an audit trail on bookkeeping changes.
That is how an accounting firm adds outsourced capacity without giving away client data.
Build a calmer filing workflow
Keep contractor docs, payment exceptions, and follow-ups tied to the actual work
Wesley is strongest when the filing problem is really a workflow problem: missing documents, unclear payment channels, and last-minute cleanup before you can trust the numbers.
Related reads
Discover adjacent articles without being sent to near-duplicate topics.

Seasonal Staff for Accounting Firms: How to Add Tax Season Capacity Without Losing Client Access Control

Customer Success: How a Pakistan Bookkeeping Team Got QuickBooks-Ready CSVs From Hard-to-Access Bank Statements
